Configure security keys on servers in a scaled environment
|
Applies to |
xDB Reporting and Content Management. |
|
Sitecore Installation Framework |
Security keys are not configured by default. |
|
Azure Toolkit |
Security keys are configured by default when they are entered into the ARM template. |
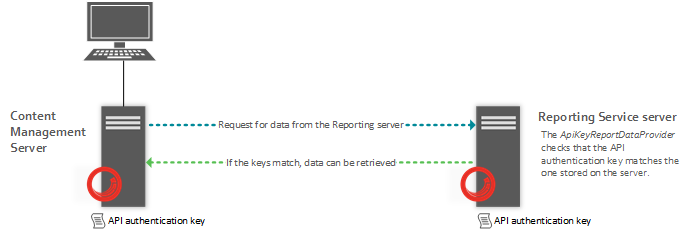
To ensure secure communication between servers in a scaled Sitecore environment, each request from a client must be authenticated on the Reporting Service server. For example, on a content management server that needs to communicate with a remote Reporting Service server. In scaled environments, only authenticated parties can gain access to data on remote servers.
For each server request, the Sitecore.Analytics.Commons.ApiKeyHttpTransportFactory class adds a custom HTTP header to the page requested. The header includes an API authentication key, which is stored in the ConnectionStrings.config file.
API authentication keys are required in Sitecore 8.2 update 1 and later.
On each server you must enter an API authentication key that can be used during the authentication process. Keys must be identical to successfully authenticate requests. For example, the key on a Reporting Service server must match the key stored on a content management server to successfully retrieve data from the Reporting Service.
The server authentication process is as follows:
-
A content management client requests data from the Reporting Service server using the
Sitecore.Analytics.Commons.ApiKeyHttpTransportFactoryclass. -
When the Reporting Service server receives the request, the
ApiKeyReportDataProviderchecks that the API authentication key from the HTTP header matches (case-sensitive) the one stored on the Reporting Service server. -
If the two keys match, the processing of the request can continue, data is retrieved and can be sent back to the content management client.
-
If the authentication keys do not match, the server responds with a 403 (Forbidden) status code.
Use HTTPS across your entire website. In the Sitecore.Xdb.Remote.Client.config file, RequireHttps is enabled by default and should remain enabled in all production environments. HTTP is not secure enough for production servers and should only be used on local testing or development instances.
This topic describes:
Configure an API authentication key
Configure an API authentication key
To configure an API authentication key:
-
Add an API authentication key to the server instance that is making the request for data from the Reporting Service server, such as to a content management server. On the content management server, navigate to the
Website\App_Configfolder and open theConnectionString.configfile. -
In the
ConnectionStrings.configfile, find thereporting.apikeyconnection string and enter an ASCII string to use as a key (default minimum length 32 characters). The key can be any combination of numerals or text. -
For example:
-
The string you choose must conform to the minimum API key length as specified in the
Sitecore.Xdb.Remote.Client.configfile,MinimalApiKeyLengthattribute. -
Add the same key to the server that will receive the request, such as a Reporting Service server. Repeat the same process by entering the API authentication key in the
ConnectionStrings.configfile.
Content management server configuration
Content management server configuration
When you set up a dedicated content management server, you must also enable the Sitecore.Xdb.Remote.Client.config file. The following table shows the default parameter settings in this file that you can adjust later, if necessary:
|
Parameter |
Description |
|---|---|
|
|
The service host URL to use in all requests. Update this if the host name of your reporting server changes. |
|
|
The name of the connection string that contains the API authentication key. |
|
|
The name of the header to include in the request. Use the same header name on both servers. For example, |
|
|
This specifies a minimum key length for the API authentication key. If it is too short, then the request will not be sent. Longer keys are more secure. |
|
|
Boolean switch set to |
These configuration parameters appear in the following section of the Sitecore.Xdb.Remote.Client.config file:
Reporting Service server configuration
Reporting Service server configuration
On the Reporting Service server, the Sitecore.Analytics.Reporting.ApiKeyReportDataProvider is defined in the <dataProvider> configuration section of the Sitecore.Xdb.Remote.Server.config file. The Sitecore.Xdb.Remote.Server.config file contains the following default parameters:
|
Parameter |
Description |
|---|---|
|
|
The name of the connection string that contains the correct API authentication key (this should match the key of the server making the request). |
|
|
The name of the header to check in the incoming server request. |
These configuration parameters appear in the following section of the Sitecore.Xdb.Remote.Server.config file: